Unlike the "open web", which is readily accessible and searchable, the deep web requires specific credentials or authorization for access. Tor bridges are special entry nodes that are not publicly listed, so they help users bypass censorship in countries where Tor is blocked. The data enters the network through an entry node, passes through one or more middle nodes, and finally leaves the network through an exit node. As the data passes through each relay (node) in the Tor network, one layer of encryption is removed, revealing the next destination for the data but not the final endpoint. When data is sent over the Tor network, it is encrypted in multiple layers.
In the ever-evolving landscape of the internet, anonymity and privacy have become critical subjects for many users. One of the most talked-about aspects of this realm is the use of .onion links, which enable access to hidden services on the Tor network. Understanding how these links function is essential for anyone interested in digital privacy, cybersecurity, or simply exploring the vast layers of the internet. This article aims to shed light on .onion links—what they are, how they work, and their implications for users.
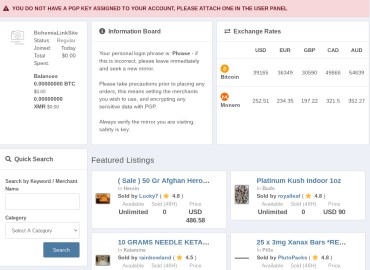
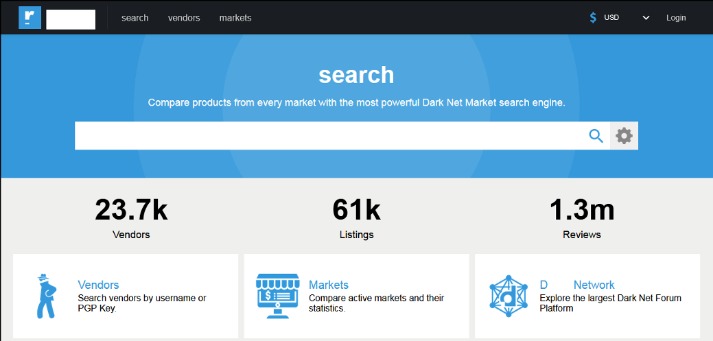
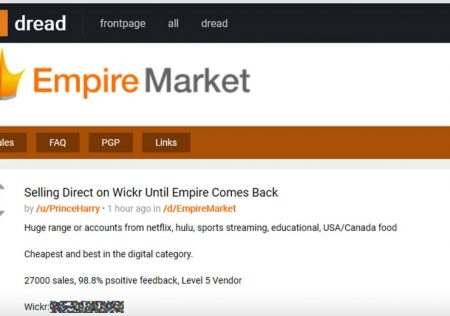
This is a directory page for some sites within the ONION network. Certain online communities share and discuss Dark Web links, though it’s crucial to verify their trustworthiness, as forums may also link to malicious sites. Candle’s index may not be as comprehensive as older search engines like Torch. Additionally, NotEvil occasionally faces takedowns or operational disruptions, given the volatile nature of Dark Web search engines. Torch’s large index makes it a popular choice for users seeking a wide array of Dark Web content. While the Dark Web is known for illicit activities like marketplaces for illegal goods and services, it also serves legal purposes.

.onion Links
.onion links are specific web addresses that can only be accessed through the Tor browser. They provide anonymity for both the user and the website, making them a popular choice for those who wish to keep their online activities private. Here’s a closer look at what .onion links entail.
What is Tor?
Tor, short for "The Onion Router," is an open-source software that enables anonymous communication on the internet. It routes your connection through multiple layers of encryption, or "onion layers," to obscure your location and usage from prying eyes, including governments and ISPs.
How Do .onion Links Work?
- Access Restricted: Only accessible through the Tor browser, which preserves anonymity for both the server and the client.
- Encryption: Data sent and received via .onion links is encrypted multiple times, protecting it from interception.
- Server Anonymity: The server hosting a .onion link is hidden, making it difficult to trace or shut down.
Common Uses of .onion Links
While .onion links often attract negative attention due to association with illegal activities, they serve various legitimate purposes, including:
- Whistleblowing: Secure platforms that allow whistleblowers to disclose information safely.
- Privacy-Focused Services: Email services, forums, and social networks that prioritize user privacy.
- Accessing Censored Information: Websites offering information that is blocked or censored in certain countries.
Risks Associated with .onion Links
While using .onion links can enhance privacy, there are notable risks to consider:
- Browsing ProPublica’s work through its .onion site works well, and the site’s very existence is a big win for privacy and free speech.
- These search engines are often the primary entry point to the internet's underbelly.
- It's divided into commercial links (from crypto services to gambling sites) and non-commercial links (like social media).
- You can now execute the file with the command ./start-tor-browser.desktop, or by double clicking the file in a file manager, to launch the connection wizard.
- Using the right search engine and following strict access practices reduces the chance of exposure to harmful content.
- Scams and Illegitimacy: The anonymity that .onion links provide can also facilitate fraudulent activities.
- Law Enforcement: Users may inadvertently access illegal content, which could lead to legal consequences.
- Malware Risks: Some .onion links may host malicious software, posing a threat to users' devices.
- You can access DuckDuckGo on the surface web, but a Tor version is also available.
- Dark web search engines do not directly expose identity, but unsafe browsing behavior can.
- Plus, many .onion websites are created to be temporary or invite-only, so they may not even be active long enough to be indexed.
- These domains are not accessible through traditional browsers or outside the Tor network.
- It's the real Tor browser and not a Tor emulator or simulator.
FAQs about .onion Links
1. Are all .onion links illegal?
No, not all .onion links are illegal. Many serve legitimate purposes, such as protecting privacy or sharing information in repressive regimes.

2. How can I access .onion links safely?
Always use the Tor browser to access .onion links and consider employing additional security practices, such as using a VPN and avoiding sharing personal information.
3. Is using .onion links completely safe?
While .onion links provide a higher level of anonymity, they are not completely foolproof. It is crucial to practice caution and stay informed about the risks involved.
In conclusion, .onion links represent a unique layer of the internet that emphasizes the importance of online privacy and anonymity. Whether used for legitimate purposes or not, understanding how to access and navigate these links can empower users in today's digital world. Always approach the dark web with caution and a well-informed mindset.