The Ares darknet represents a fascinating yet controversial segment of the internet, often shrouded in intrigue and mystery. As a part of the deep web, it operates on a level that is not indexed by conventional search engines. This article aims to provide a comprehensive overview of the Ares darknet, shedding light on its functionality, purposes, and the potential risks involved for users who venture into these obscure online spaces.
It also highlights that while MFA enhances security, it shouldn’t be blindly trusted as foolproof. The study concludes that some MFA systems are vulnerable to these attacks, often lacking context for user decisions. It introduces two threat models, the packet pausing attack and malicious endpoint attack, to exploit various MFA systems. They identified 23 distinct threats across the articles (Bezerra et al., 2022) . This platform offers ready-made phishing kits with a personal dashboard for wallet management and page creation. Attackers impersonate “the Microsoft team” and direct victims to a memorial technology hub, where they’re prompted to enter their credentials on a phishing page.
Now, can you imagine how much data they collected in this time? They also have a ton of social media accounts that post news stories and even act as recruitment tools for new members. ISIS, or sometimes it’s called ISIL, produces a ton of media content.
Ares Darknet
The Ares darknet is a peer-to-peer network that allows users to share files anonymously. Unlike mainstream platforms, it emphasizes privacy and encryption. Understanding how this network works is crucial for anyone considering exploring its contents.
How Ares Darknet Operates
- Anonymity: Users connect through specific software that masks their identities, making it difficult to trace their activities.
- File Sharing: The primary function is the sharing of various files including music, videos, software, and more.
- Privacy Protocols: The network employs various protocols to ensure that data shared among users remains confidential and secure.
- Drucker’s management principles often emphasize clear communication (Drucker, 2012) , but if communication pathways are limited for certain levels of employees, they may not receive important information that could help them identify and respond to social engineering attacks.
- The blueprint introduces a comprehensive strategy that integrates diverse security measures, underscoring the fundamental importance of safeguarding for SMEs.
- In this work, 3D-printed firearms classified as hybrids are those that have integrated non-printed parts that impact positively on the performance and reliability of the 3D-printed firearms.
- It’s just fascinating to see what happens and how they go after these people.
The Purpose of Ares Darknet
The Ares darknet serves multiple purposes, including but not limited to:
- Content Sharing: Users can share artistic projects, creative works, and educational materials.
- File Accessibility: It provides access to resources that may not be available on the surface web.
- Community Engagement: It fosters a sense of community among users who share common interests in digital content.
Risks Associated with Ares Darknet
Exploring the Ares darknet comes with inherent risks that users should be aware of:
- Legal Risks: Depending on the content shared or downloaded, individuals may inadvertently engage in illegal activities.
- Malware Threats: The network can expose users to harmful software that may compromise their devices.
- Scams: Users may encounter scams or fraudulent activities that can lead to financial loss or data breaches.
Frequently Asked Questions
1. Is using Ares darknet illegal?
Using the Ares darknet itself is not illegal; however, the content accessed may violate laws depending on jurisdiction.
2. How do I access Ares darknet?
Access generally requires specific software designed for peer-to-peer sharing and file management within the darknet.
- The scope of the operation also challenged existing capabilities for performing Political Military Assessments on time-sensitive targets.
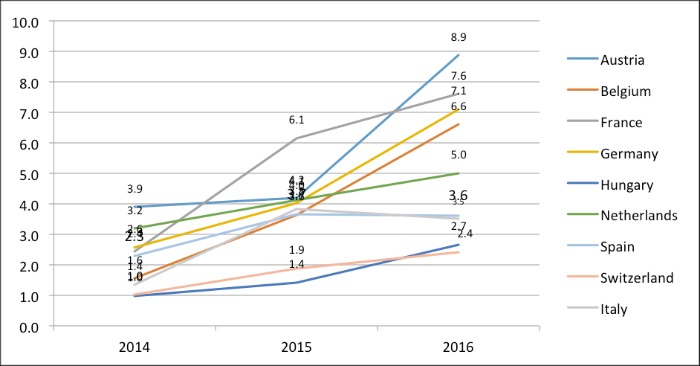
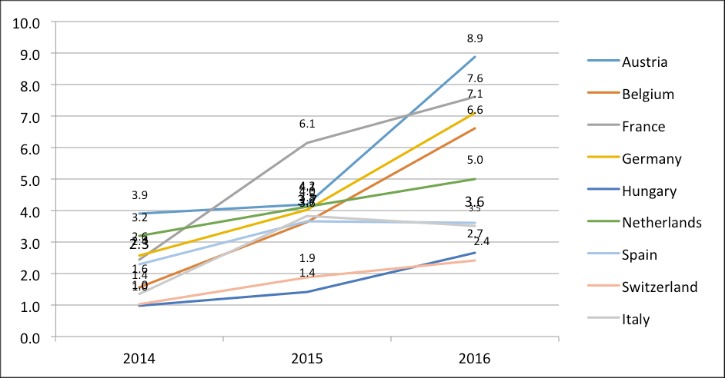
- The data were compiled into a table consisting of 85 rows representing the regions and 22 columns representing the adjusted sums of drugs in grams per region at a single time point.
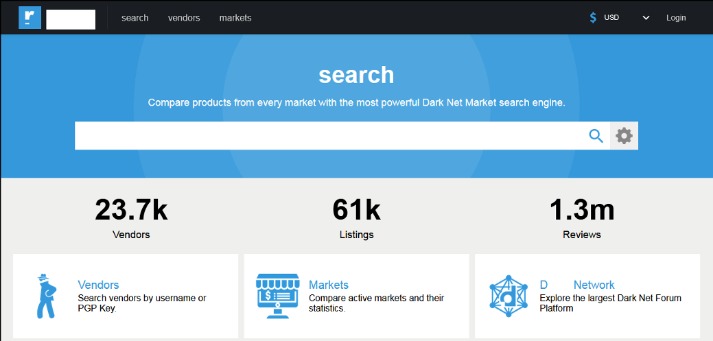
- Legally, they are limited to observing publicly accessible areas using tools like the Tor browser, without engaging in unauthorized access or illegal transactions.
- We conducted an extensive analysis of 31 official sources to assess the relevance of various indicators to drug sales on the darknet market Hydra in all 85 regions of Russia.
- An industry-wide approach is necessary to address evolving voice cloning threats while acknowledging legitimate applications and implementing safeguards (Recorded Future, n.d.) .
3. Can I remain completely anonymous on Ares darknet?

While anonymity is a key feature, no system is flawless. Users should take additional measures to enhance their privacy.
Conclusion
Understanding the Ares darknet equips individuals with the knowledge to navigate its complexities while remaining aware of the potential hazards. As with any online engagement, exercising caution, performing due diligence, and staying informed can significantly reduce risk and enhance one’s experience. Awareness is key to ensuring safe exploration of these enigmatic corners of the internet.